Introduction
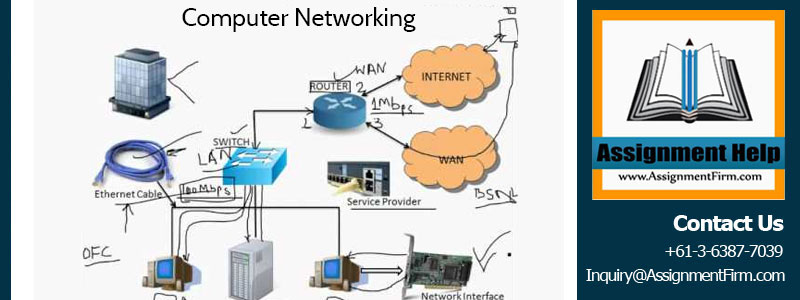
Presently, internetworks are too much complex due to the use of varying topologies in Computer Networking. The types of topologies are high meshed, point-to-point link that connects the overall network, Wide Area Network (WAN), single protocol, etc. The majority of industry in this world trends to increase the complex working environment due to more security. However, maintaining the security for internetworks needs various types of process such multiple media types and Advance Warning System (AWS) infrastructure etc.
In this research work, the selected Computer Networking is the Disruption Tolerant Networking (DTN). The program of Disruption Tolerant Networking helps in developing the reliable interplanetary internet. After creating, a long-term experiment by the Internal Space Station (ISS) within Computer Networking communication develops Disruption Tolerant Networking. Moreover, [6] cited that Disruption Tolerant Networking improves the performance of electronic communications through the storing process of data during a data interruption. However, Disruption Tolerant Networking uses the Relay station in sending the data to the destination during connection interruption in the network.
1. Overview of Disruption Tolerant Networking (DTN)
The program of Disruption Tolerant Networking (DTN) is the smaller networks. Within the internet protocols, the process of Disruption Tolerant Networking is the special purpose that overlay on top and helps in reaching the data to the destination during connection interruption. [1] argued that the system of Disruption Tolerant Networking support the interoperability in order to long disruption to the other network.
It helps in translating the multiple protocols over network communication and communicates it with the other networks. However, it has limited power as well as mobility in relation to involving the wireless communication devices. Due to use of interplanetary, Disruption Tolerant Computer Networking was developed originally. It has helped to slow down the speed of light. In the earth Disruption Tolerant Computer Networking have application that is more diverse.
A Disruption Tolerant Computer Networking is working in five different levels in network communication. The five levels of Disruption Tolerant Networking are application layer, transport layer, network layer, data link layer and physical layer.
In the application layer, Disruption Tolerant Computer Networking works in four different parts.
Bundle Protocol – This is also called Intra Disruption Tolerant Networking routing. In Disruption Tolerant Networking, bundle protocol is the core network protocol. Regarding IP in networking system, bundle protocols work as an analogous. During the linking process of different nodes, the bundle protocol retained the outbound items within the local storage place.
Delay Tolerant Payload Conditioning – The Consultative Committee for Space Data System (CCSDS) develops a new application of Delay Tolerant Payload Conditioning (DTPC) for Disruption Tolerant Computer Networking in order to improve the service and standardized within the network communication. According to [8], Delay Tolerant Payload Conditioning (DTPC) works better and performs multiple functions within the network. The source of DTPC executes properly and connects the final destination with the end-to-end network path. However, in some cases, some of the major problems have been detected such as gap in networking system and data sequencing that is present in Delay Tolerant Payload Conditioning (DTPC) to analogous of the Transmission Control Protocol (TCP). Furthermore, the Delay Tolerant Payload Conditioning (DTPC) protocols of DTN deliver the file within the network with better performance.
User Application – Within the network, DTN has multiple user applications. It not only performs to transfer the file within the network, but also it has the potentiality to long latencies. Without waiting for any quarries the applications of DTN share or distribute the information after known.
Apart from that, the transport layer of DTN contains three protocols, Transmission Control Protocol (TCP), User Network Diagram Protocol (UDP) and Licklider Transmission Protocol (LTP). The TCP protocols allow the DTN service to exchange the single end-to-end data within the network environment. As stated by [5], TCP is the excellent protocols of DTN in convergence layer. On the other hand, Licklider Transmission Protocol (LTP) is help in delivering the data of the bundle protocol from one node of TCP to another node using the system of Automatic Repeat Request (ARQ). UDP helps in retransmission within the network between the two nodes of DTN. It has the multiple network links and transfer the information or data with great speed. According to [4], UDP is the underlying link as well as service of Licklider Transmission Protocol (LTP) on the earth.
Apart from that, at the network layer IP is present and link the layer present Ethernet, various types of Fiber Distributed Data Interface (FDDI) and Wireless network connection. In the physical layer of DTN, wire is involved.
2. Disruption Tolerant Computer Networking Architecture
This reflects the architectural features of Disruption Tolerant Networking (DTN). This architectural process is guiding the various principles within the internet network.
Figure 2: Architecture of Disruption Tolerant Networking
2.1 Virtual Message Switching
The application of Disruption Tolerant Networking (DTN) is able to send the message on the arbitrary length. The application units of Disruption Tolerant Networking (DTN) act as a protocol of bundle layer that allows in transferring the data from one node to another. Within the network process bundles has various blocks that contain either data or information that deliver to the destination. Each block of bundle protocol layers acts as the purpose of containing data and information.
However, each block is found in the header of Disruption Tolerant Networking. Sometimes, the terminal blocks does not use in the bundle protocol. It is not the particular process of requirement. Instead of blocks used header to appear or display exact product. For example, the header is used instead of the block during share of digital signature. During the transmission of multiple data within the networking process, bundle protocols might be fragments into several bundles. This process is called bundle fragments. According to [3], more than two bundle blocks create a new bundle protocol in the networking system.
Endpoint identifiers help in identifying the source as well as the destination of the bundle. Endpoint identifiers are helped to identify the accurate and original source and destination in the network. However, endpoint identifiers are used in special transmission in the network. In order to multi transfer of information or data endpoint identifiers allocate various nodes of Disruption Tolerant Networking.
During the store and forward operation, IP address allocation is adopt the storing place in order to transmit the data. In addition, the architecture of Disruption Tolerant Networking is not executing or linking the data reliability or availability. In most of the cases it is identified that bundle protocol contains life indicator regarding timestamp originate. However, the bundle protocol originates the service designator and the length of data transfer layer. Use of this information bundle layer routing allows in sending the information based on a request and requirement [10].
Moreover, bundle layer data transmission process is executed during the time of significant amounts of queuing within the network. The key advantage of this key significant bundle layer protocol is appropriate process of time scheduling and path selection process. According to [2], the key elements of bundle layer are the forwarding of bundles into the destination. However, the highlighting assumption for bundle layer protocol in the network is the availability of storage and well distribution. Make the storage place sufficient due to containing more data and information in the network. Robust the bundle layer due to store the data until forwarding into next nodes of Disruption Tolerant Computer Networking .
2.2 Endpoints
In the network system, the Disruption Tolerant Computer Networking is the process of sending and receiving bundles. The application of the bundle protocol utilizes the Disruption Tolerant Networking nodes due to send or receive data and information to destination. Each node carried out various endpoints. The bundle protocol ensures the successful delivery of information based on requirement into the Disruption Tolerant Computer Networking endpoint without creating any error.
2.3 Endpoint identifiers Registrations
In the network, the endpoint identifiers using the syntax of User Resource Identifiers (URI) properly identify the Disruption Tolerant Networking (DTN) endpoints. The application of Disruption Tolerant Networking node using the particular endpoint identifiers sends the data or information to destination. However, the application of endpoint nodes systematically attempts to create a registration due to unsuccessful of sending information. For instance, in an endpoint ID the application creates itself a registration that unaccountable within the node of Disruption Tolerant Networking.
2.4 Multi-cast and Any cast
According to [7], multicast is the group delivery process that may present within the Disruption Tolerant Networking. However, it is an issue in respect of group members. In the internet network, the node of Disruption Tolerant Computer Networking considers the part of the group expressed in the network. However, during the interval, the nodes of Disruption Tolerant Networking are willing to send or receive data over network. Moreover, the application of endpoint identifiers expressed the data according to the desired results.
On the other hand, during the interval the node is currently works and receives the potential availability for long term [12]. In the network, to support the temporal group node of Disruption Tolerant Computer Networking storing the data and designs it according to requirements.
Whereas, the endpoint identifiers containing the endpoint of Disruption Tolerant Computer Networking . However, during the time of data transmission, if the size of group is more than one than the endpoint identifiers help in delivering semantic data it may be any cast or multi-cast. The bundle of group delivery, during the any-cast group delivery sends the information one node to another about their potential intend.
2.5 Priority Classes
In order to deliver the bundles from one node to another, the Disruption Tolerant Networking architecture offers various priorities such as low, medium and high. These offered priorities help in differentiating the traffic according to the desire application that affects in positive delivery. For example, the service providers of postal in Australia using a strong metaphor of priority classes fulfil the requirement of common people and deliver the data or information according to their needs and demands.
Use of Disruption Tolerant Computer Networking architecture helps in delivering the product within proper time. Within the network, the priority classes define the proper stage, segment the network into several nodes, and identify the proper path [2]. In the network, the priority classes schedule the appropriate bundles and make it in a consequence prioritization. In the network, there are three types of priority classes present: bulk, normal and expedited. All of these applications specify the proper request and send the data into proper destination.
3. Problems of Disruption Tolerant Networking
However, there are various challenges of Problems of Disruption Tolerant Networking (DTN). The shared of data is the major problems of Problems of Disruption Tolerant Networking in the networking process. During the length data, transmit the infrastructure of traditional public key is unable to verify the proper certificates in order to reliable of data. Problems of Disruption Tolerant Networking are unable to check the freshness of certificates due to rust worthy of data in the network [9]. Apart from that, regarding the Disruption Tolerant Networking, lack of global view within the network system is also a major disadvantage.
During the time of message distribution, the highest level of confusion is occurred of the resources. In the network community, the direct pertaining system of protocol with the other participant is allowed in defeating the network partitioning.
While high latency connection with the network system, various protocols is used as additional reply. It is helps in increasing the efficiency of Disruption Tolerant Networking, to deliver the message to the destination. Whereas, the cryptology process of Disruption Tolerant Networking is not feasible for the sender with the receiver. The message passing into longer distance takes time to deliver in the network [7]. Sometimes the scheduling process and the selection of the path is too much complex in the network to select in order to share the information. In the network system, loss of data from the data storage place is the major problem.
Sometimes, the inability of data raises its own problems within the network. Moreover, during the allocation of nodes misinterprets or collision of data is raised. These lead the potentiality or conflicts of public or private the data in the network system. In the forms of relay operations, Disruption Tolerant Networking is not able to fix routing. Within the wider network system, the application of Disruption Tolerant Networking sometimes may not work properly.
4. Solutions Framework Disruption Tolerant Networking (DTN)
4.1 Proposed architecture for Disruption Tolerant Network
In order to address the access control issues in DTN (Disruption Tolerant Networking), the following mechanism is workable for identify and access control. The access control mechanism of Disruption Tolerant Networking must to maintain this mechanism –
- Authentication and authorization need to be separated.
- The application of internal decision-making will be strong and support offline processing.
- Data overlap and communication exchange between the two or more nodes must to minimise.
- Implement the scalability and simplicity.
Within the mechanism of Disruption Tolerant Networking (DTN), require implementing the application and function of DTNAS (Disruption Tolerant Networking Access Server), PN (Private Network), UNSC (United Nation Security Controller), NAS (Network Access Server) and UN (United Nation).
DTNAS – This is act as a central server and coordinates with the various network servers. DTNAS generates the Common Communication Parameter (CCP) during the phase of service initialization and network registration.
UNSC – The mechanism of UNSC in DTN registers the entire private networks. Apart from that, UNSC act as a maintaining security of network registration.
NAS – The mechanism of NAS is handle the security gateway and handle the overall access control within the network. On the other hand, NAS works in generating the CCP and certificates of the Private Network [9]. However, within the network NAS verify the request validity and maintain the regional responsibilities in storing certificates of PN and CCP.
4.2 Prioritisation
The above given architecture framework provides the scheme of prioritisation. It allows the applicant to inform routers about the urgency of own packages in the network. Moreover, due to share multiple information prioritisations applies on the endpoint identifiers. It helps in multicast and any-cast communication in the network. During the multiple sharing process in the network, high risks of data overlap or data collision. However, based on the proposed architecture the prioritisation scheme is able to select the proper path and engage the routes accurately. It minimises the data overlap or data collision in network.
4.3 Content Distribution
Due to maintain bandwidth efficiency and privacy preserving the content is share and mirrors the potentiality. For example, due to share the source of news the content distribution anticipate across in a locality. It helps in improving the availability of information for the clients and reduces the direct load with the lower connectivity. Through peer-to peer sharing mechanism the content, observe the relationship between the news sources and the clients. It helps in consuming the information for client individually.
Apart from that, the content distribution provides the anonymous message board systems that helps in encrypted the message properly and broadcast it in the local mesh. Furthermore, the content distribution provides the set of mechanism that gives a proper key to decrypt the message to a client.
4.4 Broadcast
The proposed architecture of DTN (Disruption Tolerant Networking) is able to provide proper application in the computer network the multicast endpoint. According to the mention report, the endpoint identifier helps in identifying the subset of network due to the purpose of routing and message bundles. In addition, the specification of proposed mechanism for Disruption Tolerant Networking (DTN), allows in identifying the any cast and multicast respectively. The mechanism is allowed to content delivery successfully within a single recipient.
5. Results
Investigate the above study it is identify that the disruption tolerant network makes the process easy in the network through its application and mechanism. The various types of topologies and the point-to-point linking process allow in connecting the overall network and its nodes. It has a long-term equipment of internal space station. From the study, understand that disruption network works in five different levels such as physical layer, data link layer, network layer, transport layer and application layer.
Bundle protocol act as an analogous in the network system. In the application layer, Disruption Tolerant Payload Conditioning helps in improving the service. Virtual message switching transfer data and information using the bundle layer protocol. Additionally, bundle layer protocols originate the time stamp. This helps in time scheduling and selecting the appropriate path to share information. Endpoint identifier systematically develops the registration and maintains proper security.
Priority classes differentiate the traffic within the network and schedule them according to the desire application. However, various challenges of DTN (Disruption tolerant Networking) have been described in this study. The major problem in DTN is data overlapping or data collision during transfer length data or multiple accesses. Lack of global view is also key issue for Disruption tolerant Networking.
Furthermore, due to solve the issues of Disruption tolerant Networking explained solutions methods in this research. The proposed architecture for Disruption tolerant Networking is able to maintain the data overlapping and data collision during multiple accesses by the clients. The various function of proposed architecture for Disruption tolerant Networking like UNSC, DTNAS, NAS, PN, UN, etc works properly and maintain the responsibilities of generating registration and certificates of Common Communication Parameter (CCP).
5.1 Future Implementation
In order to future success of Disruption Tolerant Networking (DTN), lightweight hierarchical architecture needs to implement. The architecture of C++ is required to implementing due to validate the result. Mandatory Access Control (MAC) needs to implement within the system of Disruption Tolerant Networking. It addressed the issues. Role based Access Control needs to be implements in order to feasibility of Disruption Tolerant Networking process.
Conclusion
This case study is based the on internet working troubleshooting specifically for Disruption Tolerant Networking (DTN). At the first phase of this assignment discussed about the Disruption Tolerant Networking (DTN). Different layers of Disruption Tolerant Networking (DTN) and the function of different layers are clearly explained in this study. The general or common architecture of Disruption Tolerant Networking was given here. After discuses the architecture common problems of Disruption Tolerant Networking is described such as data overlapping during long-term process. Furthermore, talk about solution of arise problems.
Get MN503 Network Requirement Analysis And Plan Assignment Help By Professionals.


